Recent
Recent
Top Stories
Top Stories
Wildfire
Rising to the Wildfire Challenge
April 26, 2024
Recommended
Recommended
Podcasts
Line Life Podcasts
Jan. 18, 2024
Members Only Content
Home
The Macro-Impact of the Microgrid
April 24, 2024
Smart Grid
Reimagining The Future Grid
April 17, 2024
Sponsored Content
Sponsored Content
Renewables
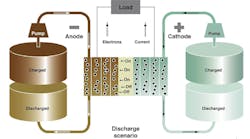
Battery Energy Storage Systems | QuickChat
April 18, 2024
Renewables
Aerial Spacer Cable in Renewables Applications
March 27, 2024
Sponsored Content
Jobs
Jobs